UFABETเข้าสู่ระบบ การเดิมพันออนไลน์ ครบวงจร ทันสมัย
UFABETเข้าสู่ระบบ เว็บอันดับ1 ฝากถอนออโต้ บริการได้มาตรฐาน ระดับพรีเมี่ยม
UFABETเข้าสู่ระบบ เว็บอันดับหนึ่ง ความมั่นคงทางการเงิน รองรับการฝาก-ถอนเงินผ่านออโต้ เพิ่มความมั่นใจตลอดการเดิมพันได้อย่างดี เล่นพนันได้เงินรางวัลได้อย่างดี เปิดให้บริการด้วยมาตรฐาน UFABETเว็บหลัก รวมความสนุกเล่นเกมพนันได้อย่างมีระดับความสมบูรณ์แบบการให้บริการผ่านระบบออนไลน์ที่สามารถเลือกวางพนันได้ตามที่ต้องการเข้าถึงความบันเทิงเล่นพนันได้อย่างดี เว็บพนันออนไลน์ แบบที่ไม่ผ่านเอเย่นต์เล่นพนันได้ง่ายสร้างทางเลือกใหม่ในการลงทุนอย่างดีที่สุด ระบบการเงินมั่นคง ฝาก-ถอนออโต้ บริการได้มาตรฐานด้วยระบบการเงินแข็งแกร่ง ทุกยอดการทำธุรกรรมรวดเร็วไม่เกินนาทีทำรายการแบบออโต้ได้มาตรฐานที่สุด ทั้งนี้การเริ่มต้นลงทุนได้ด้วยเงินขั้นต่ำ ที่จะทำให้การเดิมพันได้แต่ละครั้งมั่นใจได้ดีที่สุด ความน่าสนใจในด้านการลงทุนเพียงขั้นต่ำ 10 บาทเท่านั้น จุดเด่นของการเล่นเกมที่เริ่มต้นน้อยแต่ก็รวยได้จริง และแจ้งทำธุรกรรมได้ตลอด 24 ชม. แจ้งยอดด้วยตัวเองที่ UFABETเว็บตรง โดยไม่ต้องติดต่อเจ้าหน้าที่
UFABETเว็บหลัก สมัครแทงบอล บาคาร่า มั่นใจด้วยระบบที่ดีที่สุด
UFABETเว็บหลัก ศูนย์รวมเกมพนันออนไลน์มาตรฐานสากล ความสนุกเกมคุณภาพระดับพรีเมี่ยมคัดสรรแบรนด์ชั้นนำเข้ามาช่วยให้การเล่นพนันได้เยอะในโอกาสสร้างกำไรเกิดขึ้นได้ง่าย จากการเดิมพันเล่นเกมจากแบรนด์ชั้นนำ UFABETเว็บตรง รวมตัวไว้ให้เลือกเล่นได้เยอะที่สุด เพื่อมอบประสบการณ์สุดพิเศษตลอดการเดิมพันให้กับผู้เล่นได้เลือกวางพนันเล่นเกมที่ต้องการได้ดีที่สุด ไม่ว่าจะเป็น
- SA Gaming
- Sexy Baccarat
- Spade Gaming
- Joker Gaming
- PG Slot
และอื่นๆอีกมาก UFABETเว็บตรงไม่ผ่านเอเย่นต์ การเดิมพันเกมออนไลน์ด้วยมาตรฐานการใช้งานที่เลือกเล่นได้อย่างมั่นใจ พร้อมทั้งการดูแลของเจ้าหน้าที่คอยซัพพอร์ตสมาชิกตลอดเวลา 24 ชม. เพื่อความมั่นใจตลอดการลงทุน สล็อตufabetเว็บตรง ที่จะทำให้การเดิมพันเชื่อมั่นในการใช้งานโดยไม่ต้องกังวลเรื่องความเสี่ยงเพราะการเล่นพนันเว็บตรง UFABET ทีมงานพร้อมดูแลโดยคนไทยที่จะทำให้การเดิมพันอุ่นใจไม่ถูกทอดทิ้งเหมือนกับเว็บพนันที่ผ่านเอเย่นต์ เพราะเว็บเหล่านี้มีปัญหาการให้บริการอย่างมาก
เว็บพนันออนไลน์ UFABETที่คนเล่นเยอะที่สุด ด้วยรูปแบบที่เล่นง่าย ทันสมัย
สำหรับการเลือกใช้งาน เว็บพนันออนไลน์ ยอดนิยมufabetเว็บตรง เข้าร่วมสนุกในการเล่นพนันออนไลน์เว็บตรงที่เพิ่มความมั่นใจได้ว่าการเล่นพนันแต่ละครั้ง มีช่องทางการเดิมพันได้เปรียบในการลงทุนมากสุด เลือกวางพนันเกมที่ชื่นชอบได้อย่างง่าย เว็บยูฟ่าเบท ความสนุกในการเล่นพนันที่จะทำให้การเดิมพันมีโอกาสของการสร้างรายได้ให้กับตัวเองได้เงินรางวัลตามจริง สมัครยูฟ่าเบท ทำให้การเดิมพันแต่ละครั้งได้เห็นช่องทางการทำเงินได้ง่ายเพิ่มความเชื่อมั่นตลอดการลงทุนที่คุณไม่ควรพลาด บริการวางเดิมพันแบบครบวงจรเว็บพนันครบทุกประเภททุกชนิด ทางเข้าUFABET สามารถรองรับทุกระบบการใช้งาน และมีฐานผู้เล่นและสมาชิกให้การยอมรับเลือกเล่นอย่างต่อเนื่องทั้งรองรับภาษาไทย ภาษาอังกฤษ และมีภาษาอื่นๆให้เลือกใช้งาน เข้าสู่ระบบUFABET ที่การันตีเป็นสุดยอดเว็บพนันออนไลน์ยอดฮิต เป็นที่นิยมทั้งในกลุ่มนักพนันและบุคคบทั่วไปที่ให้ความสนใจลงทุนเดิมพันออนไลน์ กับเว็บพนันที่มีความเป็นมาตรฐานและปลอดภัยในการลงทุน

เว็บไซต์พนันออนไลน์UFABET ทายใบเหลืองใบแดงแบบสด ๆ
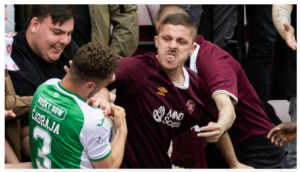
การทายใบเหลืองใบแดงออนไลน์ ได้รับความนิยมไม่น้อยที่เว็บไซต์แทงบอลออนไลน์ UFABETเข้าสู่ระบบ เปิดให้ทายผลแบบสูงต่ำถือว่าเป็นประเภทการเดิมพัน ที่ผู้เล่นทายจำนวนรวมของใบเตือนที่กรรมการผู้ตัดสินแจกใบเหลือง ใบแดง ให้กับผู้เล่นทั้งสองทีมในระหว่างการแข่งขัน โดยเทียบจำนวนรวม จากค่ากลางที่เว็บพนันเป็นผู้กำหนดราคากลางขึ้นมา UFABETเว็บหลัก ผลตัดสินแพ้ชนะไม่มีผลต่อการเดิมพันแต่อย่างใด เพราะนับตามจำนวนใบเหลือง ใบแดงที่เกิดขึ้นจริงในการแข่งขันเท่านั้น การแทงบอลออนไลน์ แบบทายใบเหลือง ใบแดง แบบสูงต่ำ มีให้เลือกวางเดิมพันได้หลายแบบที่เว็บไซต์แทงบอลออนไลน์ UFABETเว็บแม่ สามารถเลือกทายได้ทั้งแบบครึ่งแรก และเต็มเวลา 90 นาที รวมถึงการทายผลรวมเป็นแบบคู่คี่ UFABETเว็บตรงไม่ผ่านเอเย่นต์ ซึ่งจะเป็นรูปแบบการทายผลรวมใบเตือน ในครึ่งแรกหรือแบบเต็มเวลา เมื่อสรุปผลการแจกใบเตือนได้ทั้งหมดกี่ใบ สล็อตUFABETเว็บตรง อีกหนึ่งรูปแบบการทายผลที่ไม่ยาก และมีโอกาสทำเงินรางวัลได้ง่ายมาก การแทงใบเตือนใบแรกหรือใบสุดท้าย อีกหนึ่งประเภทการทายผลออนไลน์ ที่น่าสนใจที่เว็บไซต์แทงบอลออนไลน์ UFABETเว็บตรง เปิดให้เดิมพันทีมที่ตัวเองคิดว่าจะได้รับใบเตือนแรก หรือใบเตือนใบสุดท้ายของเกมแข่งขัน ซึ่งการเลือกวางเดิมพันประเภทนี้ไม่นับสีใบเตือนว่าเป็นเหลืองหรือแดง ถือว่าเป็นอีกหนึ่งประเภทการเดิมพัน www.ufabet.com ที่ตื่นเต้นไม่น้อย หากเลือกดูบอลสดจะทำให้การทายผลใบเตือนประเภทนี้ ทำเงินได้ง่ายยิ่งขึ้น
UFABETเว็บหลัก รูปแบบการแทงบอลออนไลน์หลากหลาย ครบวงจรที่สุด
ทายผลแบบพนันใบเหลืองใบแดง UFABETเข้าสู่ระบบ ค่อนข้างทำเงินได้ง่าย หากรู้จักการวิเคราะห์อย่างมีประสิทธิภาพพร้อมกับสไตล์การเล่นของทีมที่เข้าร่วม นอกจากนี้การเรียนรู้วิธีเล่นแต่ละคนในทีมเป็นอย่างไร การเรียนรู้บุคลิกของผู้ตัดสิน UFABETเว็บหลักมือถือ เป็นสิ่งที่สำคัญไม่น้อย แต่ละแมตช์ผู้ตัดสินอาจมีความเข้มงวดที่ต่างกัน ทำให้การแจกใบเหลืองหรือใบแดง มีความต่างกันออกไปโดยที่เว็บไซต์ แทงบอลออนไลน์ หากเลือกการทายใบเตือน ก็ต้องดูองค์ประกอบหลักเพื่อการเดิมพันออนไลน์ได้อย่างแม่นยำยิ่งขึ้น หากต้องการทำเงินจากการทายใบเเหลืองใบแดงที่เว็บไซต์แทงบอลออนไลน์ UFABETเว็บตรงไม่ผ่านเอเย่นต์ ควรเลือกโปรแกรมการแข่งขันออนไลน์ให้เหมาะสม เพราะเกมการแข่งขันในแต่ละลีกมีความต่างกันออกไป เว็บพนันที่ดีที่สุด โดยปกติแล้วเกมทัวร์นาเมนต์หรือเกมกระชับมิตรเป็นแมตช์ที่มีความหนาแน่น ของการแจกใบเตือนน้อย สำหรับการแข่งขันในลีกมีโอกาสเกิดขึ้นได้ง่าย หากเป็นแมตช์สำคัญหรือนักชิงถือว่าเป็นแมตช์ ที่มีแจกใบเตือนได้บ่อย ทำให้การเลือกรายการแข่งขันมีผลต่อการแทงใบเหลืองใบแดง เว็บแทงบอลออนไลน์ ใครที่ต้องการทำกำไรชัวร์ ๆ ควรเลือกรายการแข่ง ให้เหมาะสมจึงจะการรันตีทำเงินได้จริง

UFABET ดูบอลสด แทงบอลสดในเว็บเดียว
แทงบอลสด แทงบอลออนไลน์ รูปแบบการแทงบอลออนไลน์ อีกหนึ่งประเภทที่เรียกความสนใจเข้าร่วมสนุกในการเดิมพันได้อย่างมาก สามารถเลือกวางพนันได้ง่ายที่เว็บไซต์แทงบอลออนไลน์UFABET เลือกเดิมพัน ในขณะเกมกำลังแข่งขันยิ่งเพิ่มโอกาสสร้างกำไรเกิดขึ้นได้อย่างง่าย ทำให้การ แทงบอลUFABET ระหว่างเกมกำลังแข่งขัน มีส่วนช่วยให้การลงทุน แต่ละคนสามารถเน้นทำกำไรได้ง่ายกว่า เว็บพนันUFABET จึงเป็นรูปแบบการเดิมพัน ที่คนไทยส่วนใหญ่เลือกใช้งานกันมากสุด ประเภทแทงบอลสดออนไลน์ คือการเล่นพนันบอลอย่างหนึ่งที่ เว็บแทงบอลออนไลน์ เปิดให้บริการนักพนัน ซึ่งสามารถเข้าแทงบอลประเภทต่าง ๆ ได้ในระหว่างเกมกำลังแข่งขัน ซึ่งต่างจากการแทงบอลทั่วไปหรือเจ้ามือโต๊ะบอลไม่เปิดรับแทงบอล ในคู่ที่เริ่มแข่งแล้วการ แทงบอลสด ในเกมที่กำลังแข่งขันมีรูปแบบการถ่ายทอดสดจะทำให้การลุ้นผลบอลได้สนุกมากขึ้น สามารถเพิ่มโอกาสทำเงินได้มากขึ้น โอกาสชนะ และทำเงินได้ง่ายมากการ แทงบอลสดออนไลน์ ยังมีรูปแบบการแทงที่ได้รับความนิยมสูงสุดคือแฮนดิแคป เพราะอัตราต่อรองที่เว็บไซต์แทงบอลออนไลน์ UFABETเว็บหลัก เปิดให้หลายราคาให้เลือก ในแต่ละคู่ บางคู่อาจมีมากถึง 2-3 แบบ ทำให้การเลือกแทงบอลสดเป็นอีกหนึ่งรูปแบบการลงทุนที่ช่วยให้นักพนัน สามารถสร้างรายได้ให้กับตัวเองได้ลุ้นการทำเงินเกิดขึ้นได้จริง เว็บพนันบอลUFABET ความพิเศษของการเล่นพนันที่ไม่ยุ่งยากเพราะลุ้นผลบอลสด วิเคราะห์บอลได้ง่าย เพิ่มความแม่นยำในการเล่นมากขึ้น
แทงบอลสด เว็บพนันUFABET เว็บตรงต่างประเทศ
นอกจากนี้การแทงบอลสดออนไลน์ สามารถเลือกวางเดิมพันได้หลายแบบ โดยที่ เว็บไซต์แทงบอลออนไลน์ แทงบอลสดUFABET เปิดให้แทงแบบราคาต่อรอง , สกอร์สูงต่ำ , ทายจำนวนใบเหลือง ใบแดง , ทายจำนวนลูกเตะมุม รูปแบบการแทงบอลสด แทงบอลสดยังไง สามารถวางพนันได้หลายประเภท ยิ่งทำให้การแทงบอลแต่ละครั้ง ไม่ได้ยุ่งยากแถมยังมีโอกาสสร้างรายได้ให้กับตัวเองได้เงินรางวัลมากขึ้นกว่าเดิม เว็บพนันบอล ที่สำคัญสามารถวิเคราะห์เกมแข่งขัน ในทีมนั้น ๆ ได้ง่ายขึ้น รูปแบบการแทงบอลสด ทายผลระหว่างการแข่งขัน ที่ช่วยให้การเดิมพันได้เห็นผลกำไรเกิดขึ้นได้ง่ายที่เว็บไซต์แทงบอลออนไลน์UFABET การแทงสด เปิดให้แทงบอลได้หลายประเภท เท่ากับว่าเป็นโอกาสพิเศษ ที่จะทำให้การเล่น เว็บพนันออนไลน์ ไม่ยุ่งยากที่จะสร้างรายได้ให้กับตัวเองด้วยการเลือกรูปแบบแทงบอลสดให้เหมาะสมเพียงเท่านี้ ก็พร้อมลุ้นการเดิมพันได้อย่างแม่นยำ ยิ่งทำให้การเล่นพนันไม่กดดันหรือมีความเสี่ยงใด มองสถานการณ์ของทีม ก็วางเดิมพันได้แม่นยำ ถือว่าการแทงบอลสดมีโอกาสชนะทำกำไรได้ง่ายมาก
UFABETเว็บแทงบอลออนไลน์ ราคาต่อรองยุติธรรม
เว็บพนันบอลมาตรฐาน เป็นที่ยอมรับในวงการพนันอย่างดีที่สุด เลือกแทงบอลทายผลประเภทต่าง ๆ อย่างมั่นใจ ด้วยราคาต่อรองอย่างยุติธรรมที่สุด โดยที่เว็บไซต์แทงบอลออนไลน์UFABET สามารถเลือกวางเดิมพันออนไลน์ ได้อย่างสบายใจ ด้วยมาตรฐานให้บริการ ระบบเดิมพัน เข้าสู่ระบบUFABET มีความสมบูรณ์ที่สุด ได้รับความไว้วางใจจากผู้เล่นชาวไทยอย่างมาก การเดิมพันผ่าน เว็บแทงบอลเว็บตรง สร้างความเชื่อมั่นในด้านการลงทุน ที่จะทำให้การแทงบอลลุ้นผลกำไรเกิดขึ้นได้กับทุกคน แทงบอลออนไลน์ผ่านเว็บตรง ไม่ผ่านเอเย่นต์หรือตัวแทนใด ๆ สร้างความเชื่อมั่นในการเล่นพนันอย่างมาก โดยที่คุณไม่ต้องกังวลใจเมื่อใช้บริการ เว็บไซต์แทงบอลออนไลน์UFABET สามารถเลือกการใช้งานได้อย่างสบายใจอัตราต่อรองที่ยุติธรรมที่สุด UFABETเว็บแม่ มีความเป็นกลางที่สุด เพื่อการแทงบอลได้อย่างมั่นใจในการลงทุนออนไลน์ เพื่อลุ้นทำกำไรเกิดขึ้นได้ง่าย หากต้องการแทงบอลเพื่อเอาเงินรางวัลใ นแต่ละครั้งไม่ยากอย่างที่คิด
UFABETเว็บตรง ไม่ผ่านเอเย่นต์ ราคาน้ำดีที่สุด
อัพเดทราคาต่อรองตลอดเพื่อความยุติธรรมไม่ว่าจะเลือก แทงบอลออนไลน์ ครั้งใด ก็เดิมพันได้อย่างมั่นใจ ราคาอัพเดทตลอด ทำให้การแทงบอลแต่ละประเภท สามารถวางพนันได้มั่นใจมากขึ้นเว็บไซต์แทงบอลออนไลน์ UFABETเข้าสู่ระบบ เป็นเว็บที่มีความพร้อมเรื่องการอัพเดทราคา ความพิเศษของการเล่นพนัน กับเว็บตรงเรื่องราคาต่อรองยุติธรรมและเลือกราคาได้ 2-3 แบบ ทำให้การแทงบอลมีโอกาสทำเงินรางวัลได้ง่าย เว็บแทงบอลที่ดีที่สุด กับราคาที่เราเลือกได้ตามความเหมาะสม การเลือกใช้บริการเว็บพนันมาตรฐาน ที่จะทำให้การแทงบอลได้ลุ้นรางวัลเกิดขึ้นง่าย การใช้งานเว็บไซต์แทงบอลออนไลน์UFABET เว็บพนันบอลออนไลน์ที่ดีที่สุด เป็นเว็บพนันที่ดูแลระบบ และคุณภาพการเดิมพันให้ได้มาตรฐานสูงสุด โดยไม่เอารัดเอาเปรียบนักพนัน การพัฒนาเพื่อการใช้งานให้เหมาะสมกับคนไทย สามารถเข้าร่วมเดิมพันออนไลน์ได้อย่างมั่นใจ เว็บพนันถูกกฎหมาย การสร้างเว็บแทงบอลให้มีคุณภาพไม่เหมือนกับใคร ทำให้การเดิมพันในแต่ละครั้ง มั่นใจตลอดการลงทุนที่ไม่จำกัดเวลา เลือกใช้งานเพื่อเข้าร่วมสนุกในการเดิมพัน ได้อิสระมีโปรแกรมแข่งครบ ความนิยมการแทงบอลออนไลน์ผ่านเว็บตรง เว็บพนันบอลไม่ผ่านเอเย่นต์ ที่มีความพร้อมในด้านการลงทุนให้ใช้งานมากสุด เว็บไซต์แทงบอลออนไลน์UFABETทางเลือกที่ตอบโจทย์ความต้องการได้อย่างดี การสร้างรายได้ออนไลน์ให้กับตัวเอง วิธีแทงบอลออนไลน์ ได้ลุ้นผลกำไรเกิดขึ้นได้เยอะ ความสนุกในการเล่นพนันผ่านมาตรฐานการเดิมพัน อัพเดทราคาต่อรองไวมี โปรแกรมบอล ให้เลือกเล่นพนันได้เยอะที่สุด ไม่ว่าจะเป็นมืออาชีพ หรือมือสมัครเล่นก็ร่วมเล่นพนันเพื่อต้องการหารายได้เกิดขึ้นได้ง่าย ๆ ในทุกวัน